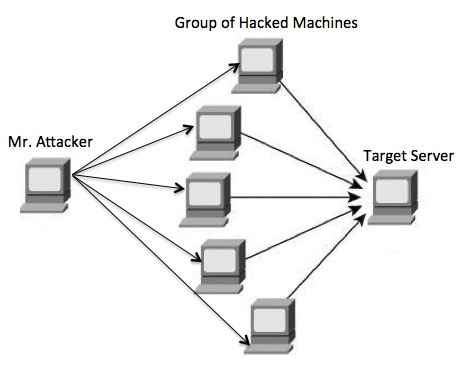
21D DoS Tools | DoS Attack using Metasploit | LOIC Tool for DoS Attack | DoS Countermeasures - YouTube

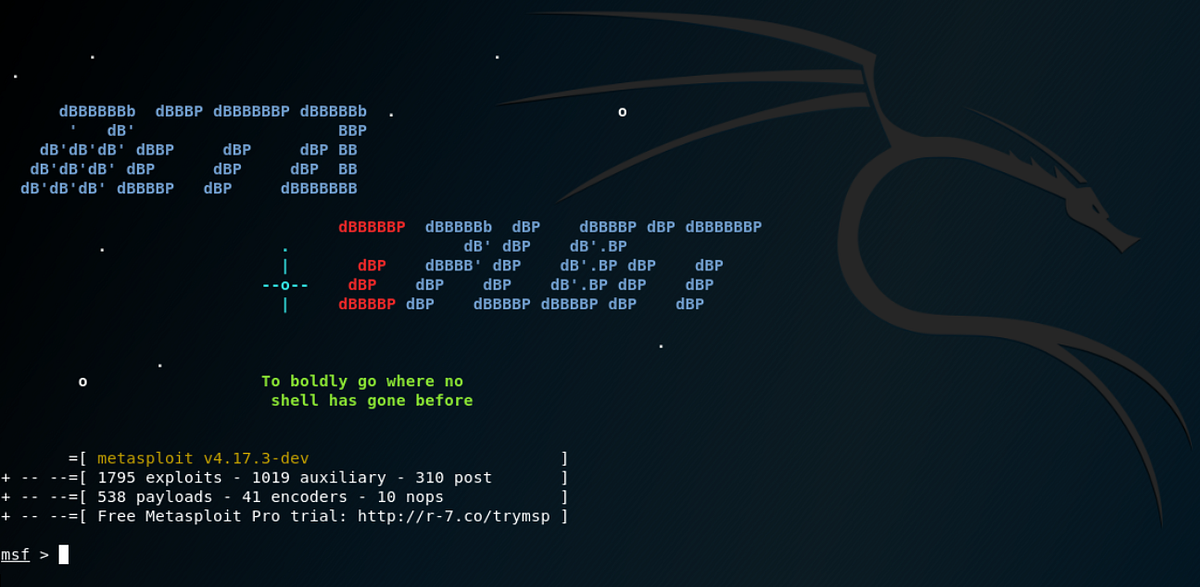
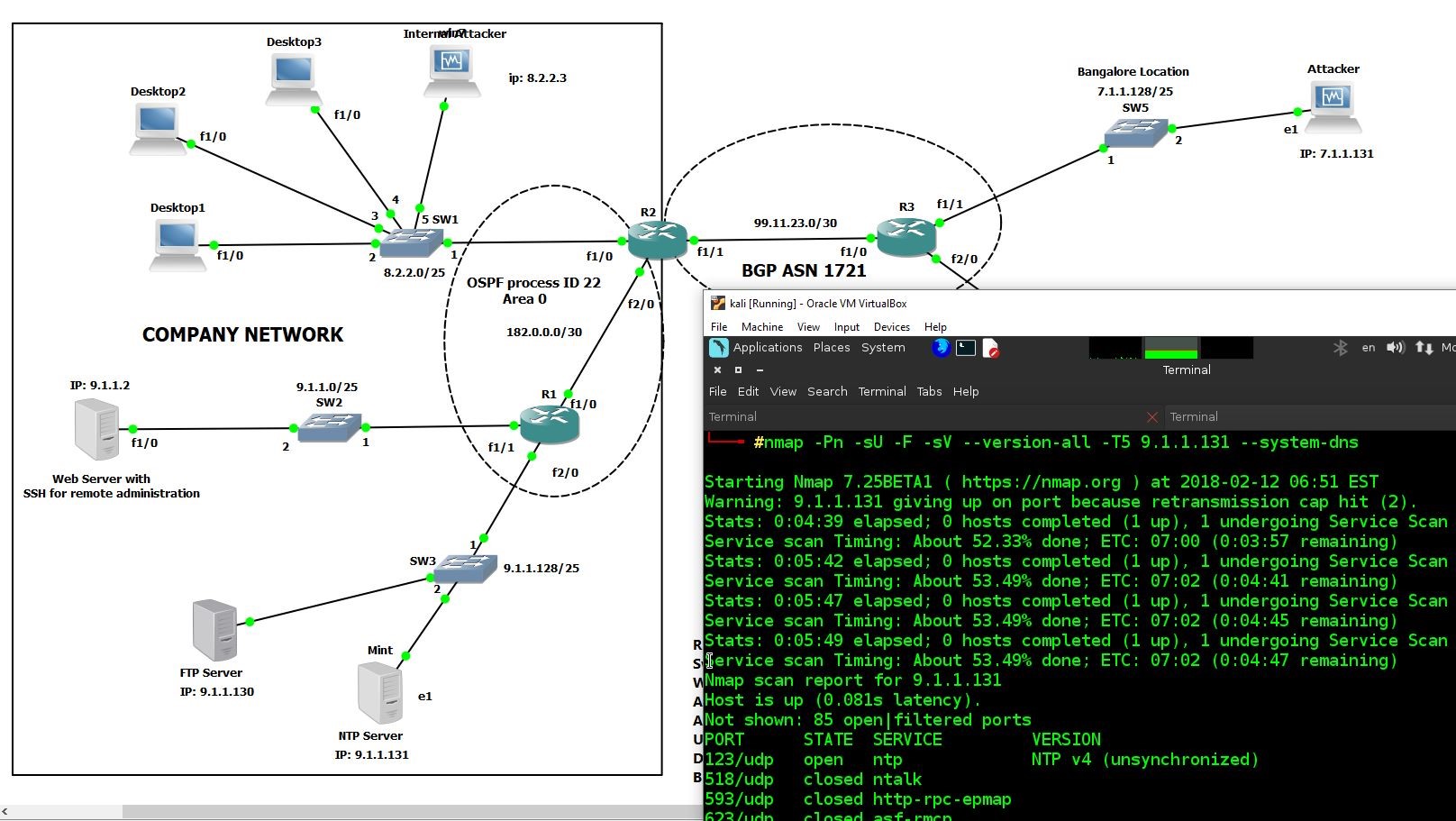
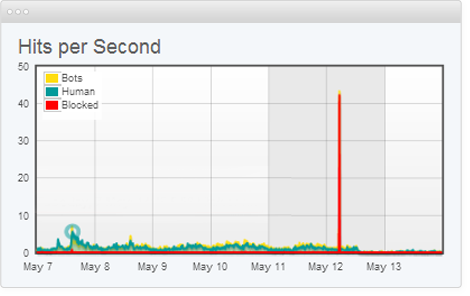
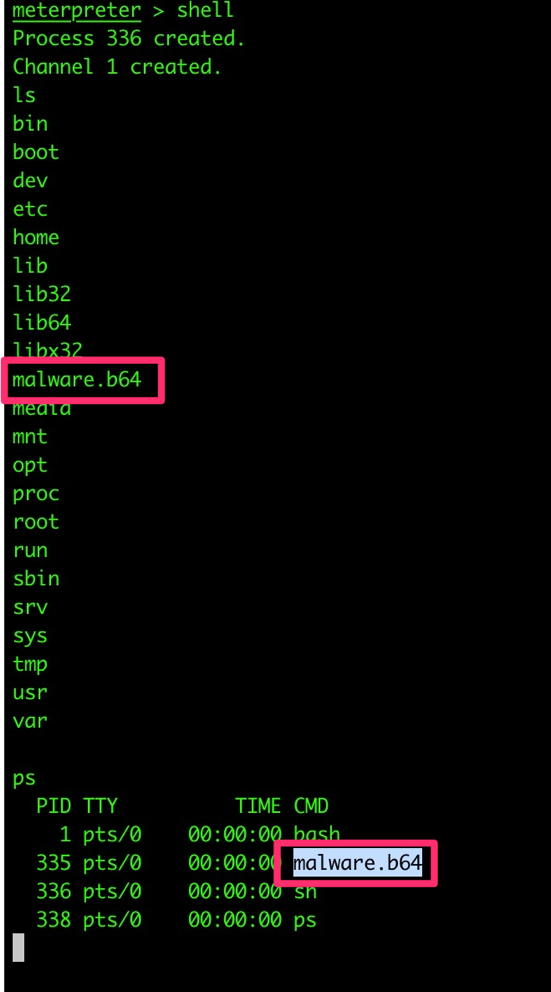
DOS) Denial-of-Service attack on Windows 2008 R2 server and Windows 7 with Metasploits on Kali Linux – darkMORE Ops

21D DoS Tools | DoS Attack using Metasploit | LOIC Tool for DoS Attack | DoS Countermeasures - YouTube